3.8 KiB
| type | stage | group | info |
|---|---|---|---|
| reference, howto | Manage | Authentication and Authorization | To determine the technical writer assigned to the Stage/Group associated with this page, see https://about.gitlab.com/handbook/engineering/ux/technical-writing/#assignments |
Restrict allowed SSH key technologies and minimum length (FREE SELF)
ssh-keygen allows users to create RSA keys with as few as 768 bits, which
falls well below recommendations from certain standards groups (such as the US
NIST). Some organizations deploying GitLab need to enforce minimum key
strength, either to satisfy internal security policy or for regulatory
compliance.
Similarly, certain standards groups recommend using RSA, ECDSA, ED25519, ECDSA_SK, or ED25519_SK over the older DSA, and administrators may need to limit the allowed SSH key algorithms.
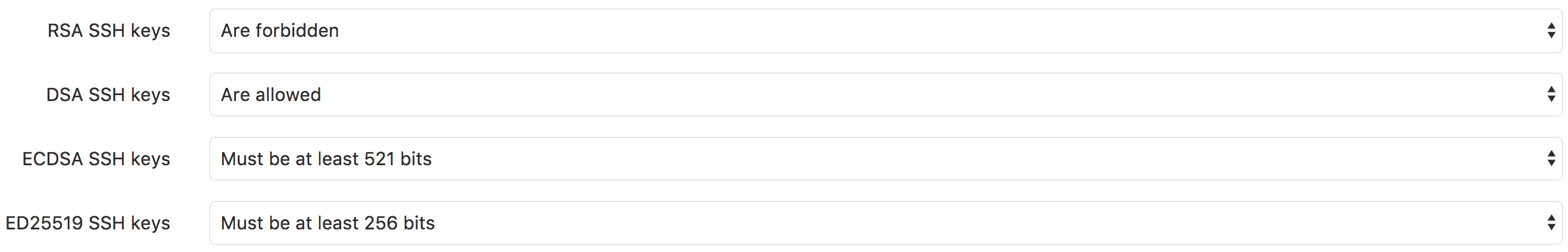
GitLab allows you to restrict the allowed SSH key technology as well as specify the minimum key length for each technology:
-
On the top bar, select Menu > Admin.
-
On the left sidebar, select Settings > General (
/admin/application_settings/general). -
Expand the Visibility and access controls section:
If a restriction is imposed on any key type, users cannot upload new SSH keys that don't meet the requirement. Any existing keys that don't meet it are disabled but not removed and users cannot pull or push code using them.
An icon is visible to the user of a restricted key in the SSH keys section of their profile:
Hovering over this icon tells you why the key is restricted.
Default settings
By default, the GitLab.com and self-managed settings for the supported key types are:
- RSA SSH keys are allowed.
- DSA SSH keys are forbidden (since GitLab 11.0).
- ECDSA SSH keys are allowed.
- ED25519 SSH keys are allowed.
- ECDSA_SK SSH keys are allowed (GitLab 14.8 and later).
- ED25519_SK SSH keys are allowed (GitLab 14.8 and later).
Block banned or compromised keys (FREE)
Introduced in GitLab 15.1 with a flag named
ssh_banned_key. Enabled by default.
FLAG:
On self-managed GitLab, by default this feature is available. To hide the feature per user,
ask an administrator to disable the feature flag named ssh_banned_key.
On GitLab.com, this feature is available.
When users attempt to add a new SSH key to GitLab accounts, the key is checked against a list of SSH keys which are known to be compromised. Users can't add keys from this list to any GitLab account. This restriction cannot be configured. This restriction exists because the private keys associated with the key pair are publicly known, and can be used to access accounts using the key pair.
If your key is disallowed by this restriction, generate a new SSH key pair to use instead.