47 KiB
| stage | group | info | type |
|---|---|---|---|
| Create | Gitaly | To determine the technical writer assigned to the Stage/Group associated with this page, see https://about.gitlab.com/handbook/engineering/ux/technical-writing/#designated-technical-writers | reference |
Gitaly Cluster
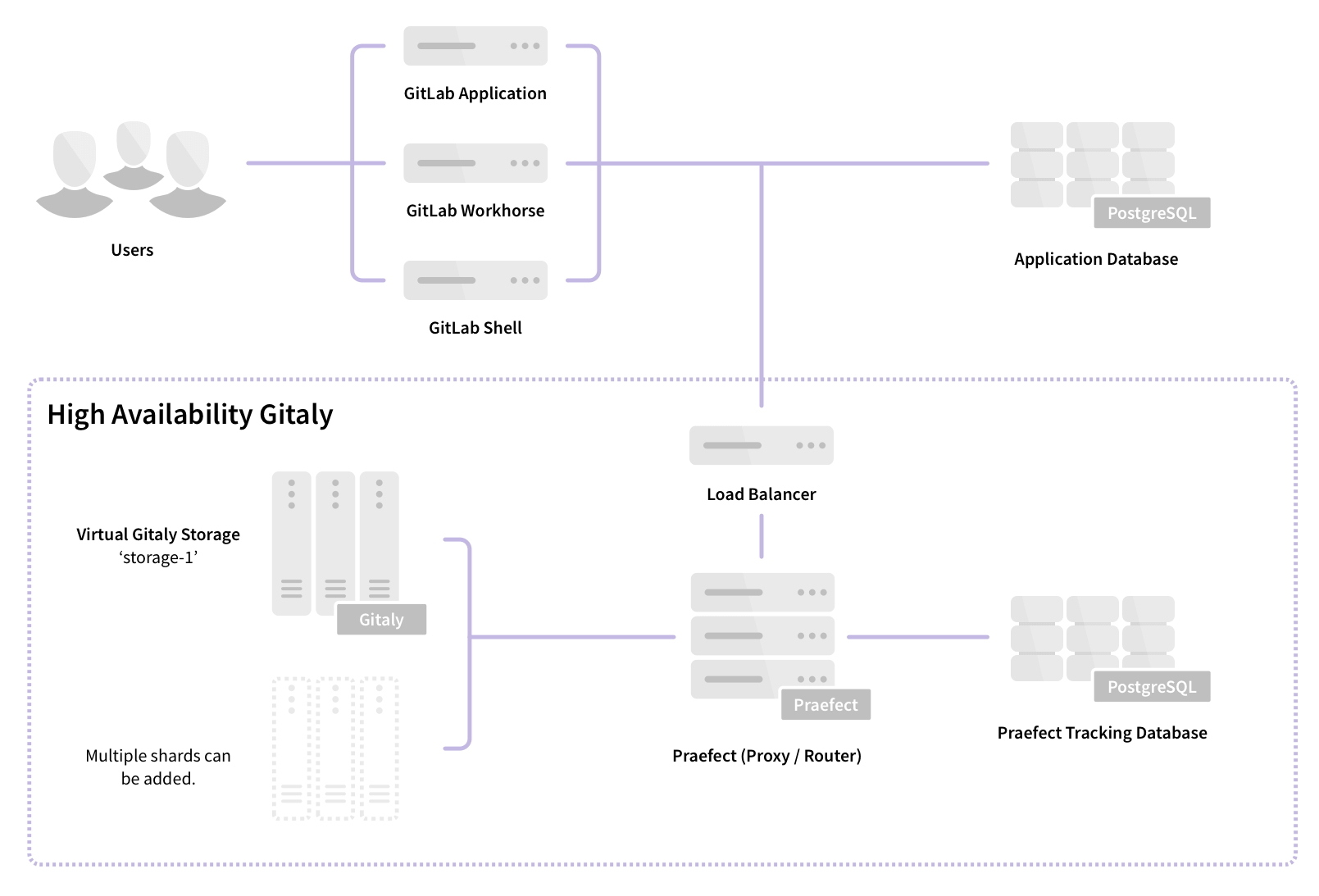
Gitaly, the service that provides storage for Git repositories, can be run in a clustered configuration to increase fault tolerance. In this configuration, every Git repository is stored on every Gitaly node in the cluster. Multiple clusters (or shards), can be configured.
NOTE: Note: Gitaly Clusters can be created using GitLab Core and higher tiers. However, technical support is limited to GitLab Premium and Ultimate customers only. Not available in GitLab.com.
Praefect is a router and transaction manager for Gitaly, and a required component for running a Gitaly Cluster.
Using a Gitaly Cluster increase fault tolerance by:
- Replicating write operations to warm standby Gitaly nodes.
- Detecting Gitaly node failures.
- Automatically routing Git requests to an available Gitaly node.
The availability objectives for Gitaly clusters are:
-
Recovery Point Objective (RPO): Less than 1 minute.
Writes are replicated asynchronously. Any writes that have not been replicated to the newly promoted primary are lost.
Strong consistency can be used to avoid loss in some circumstances.
-
Recovery Time Objective (RTO): Less than 10 seconds.
Outages are detected by a health checks run by each Praefect node every second. Failover requires ten consecutive failed health checks on each Praefect node.
Faster outage detection is planned to improve this to less than 1 second.
The current version supports:
- Eventual consistency of the secondary replicas.
- Automatic failover from the primary to the secondary.
- Reporting of possible data loss if replication queue is non empty.
- Marking the newly promoted primary read only if possible data loss is detected.
Follow the HA Gitaly epic for improvements including horizontally distributing reads.
Cluster or shard
Gitaly supports multiple models of scaling:
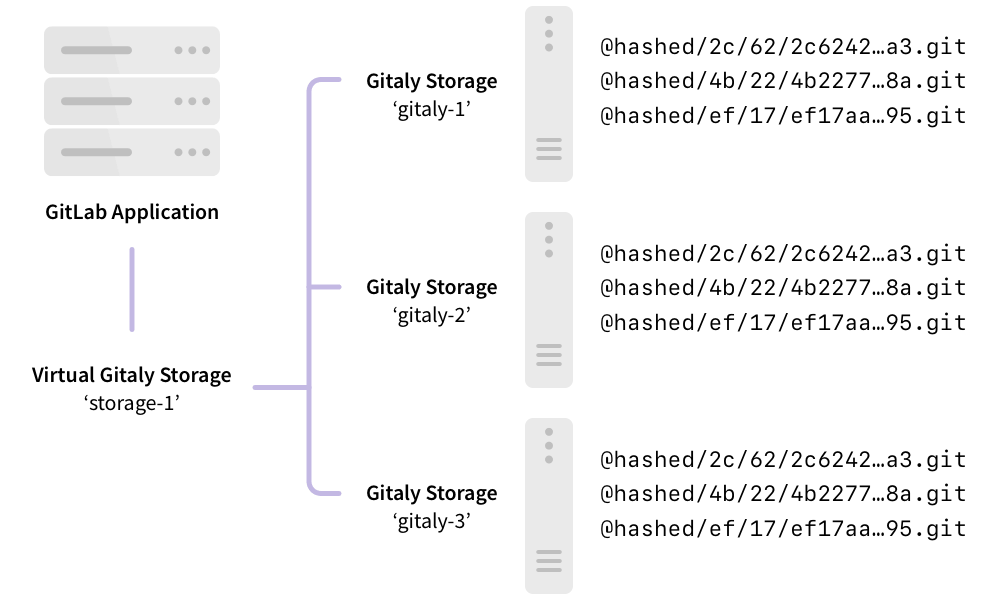
- Clustering using Gitaly Cluster, where each repository is stored on multiple Gitaly nodes in the cluster. Read requests are distributed between repository replicas and write requests are broadcast to repository replicas.
- Sharding using repository storage paths, where each repository is stored on the assigned Gitaly node. All requests are routed to this node.
| Cluster | Shard |
|---|---|
 |
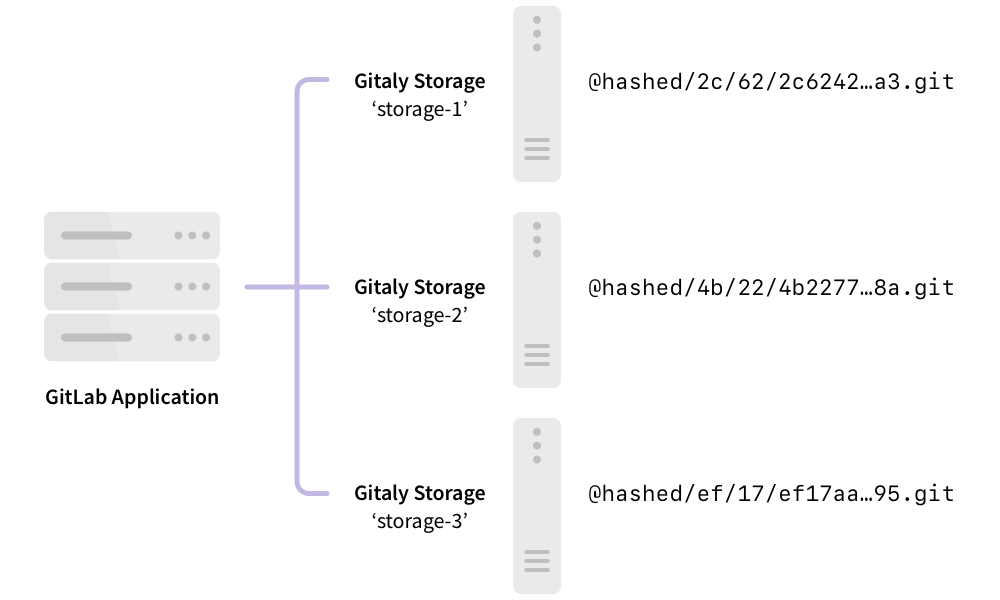 |
Generally, Gitaly Cluster can replace sharded configurations, at the expense of additional storage needed to store each repository on multiple Gitaly nodes. The benefit of using Gitaly Cluster over sharding is:
- Improved fault tolerance, because each Gitaly node has a copy of every repository.
- Improved resource utilization, reducing the need for over-provisioning for shard-specific peak loads, because read loads are distributed across replicas.
- Manual rebalancing for performance is not required, because read loads are distributed across replicas.
- Simpler management, because all Gitaly nodes are identical.
Under some workloads, CPU and memory requirements may require a large fleet of Gitaly nodes and it can be uneconomical to have one to one replication factor.
A hybrid approach can be used in these instances, where each shard is configured as a smaller cluster. Variable replication factor is planned to provide greater flexibility for extremely large GitLab instances.
Requirements for configuring a Gitaly Cluster
The minimum recommended configuration for a Gitaly Cluster requires:
- 1 load balancer
- 1 PostgreSQL server (PostgreSQL 11 or newer)
- 3 Praefect nodes
- 3 Gitaly nodes (1 primary, 2 secondary)
See the design document for implementation details.
Setup Instructions
If you installed GitLab using the Omnibus package (highly recommended), follow the steps below:
- Preparation
- Configuring the Praefect database
- Configuring the Praefect proxy/router
- Configuring each Gitaly node (once for each Gitaly node)
- Configure the load balancer
- Updating the GitLab server configuration
- Configure Grafana
Preparation
Before beginning, you should already have a working GitLab instance. Learn how to install GitLab.
Provision a PostgreSQL server (PostgreSQL 11 or newer). Configuration through the Omnibus GitLab distribution is not yet supported. Follow this issue for updates.
Prepare all your new nodes by installing GitLab.
- 1 Praefect node (minimal storage required)
- 3 Gitaly nodes (high CPU, high memory, fast storage)
- 1 GitLab server
You will need the IP/host address for each node.
LOAD_BALANCER_SERVER_ADDRESS: the IP/host address of the load balancerPOSTGRESQL_SERVER_ADDRESS: the IP/host address of the PostgreSQL serverPRAEFECT_HOST: the IP/host address of the Praefect serverGITALY_HOST: the IP/host address of each Gitaly serverGITLAB_HOST: the IP/host address of the GitLab server
If you are using a cloud provider, you can look up the addresses for each server through your cloud provider's management console.
If you are using Google Cloud Platform, SoftLayer, or any other vendor that provides a virtual private cloud (VPC) you can use the private addresses for each cloud instance (corresponds to “internal address” for Google Cloud Platform) for PRAEFECT_HOST, GITALY_HOST, and GITLAB_HOST.
Secrets
The communication between components is secured with different secrets, which are described below. Before you begin, generate a unique secret for each, and make note of it. This will make it easy to replace these placeholder tokens with secure tokens as you complete the setup process.
GITLAB_SHELL_SECRET_TOKEN: this is used by Git hooks to make callback HTTP API requests to GitLab when accepting a Git push. This secret is shared with GitLab Shell for legacy reasons.PRAEFECT_EXTERNAL_TOKEN: repositories hosted on your Praefect cluster can only be accessed by Gitaly clients that carry this token.PRAEFECT_INTERNAL_TOKEN: this token is used for replication traffic inside your Praefect cluster. This is distinct fromPRAEFECT_EXTERNAL_TOKENbecause Gitaly clients must not be able to access internal nodes of the Praefect cluster directly; that could lead to data loss.PRAEFECT_SQL_PASSWORD: this password is used by Praefect to connect to PostgreSQL.
We will note in the instructions below where these secrets are required.
PostgreSQL
NOTE: Note: Do not store the GitLab application database and the Praefect database on the same PostgreSQL server if using Geo. The replication state is internal to each instance of GitLab and should not be replicated.
These instructions help set up a single PostgreSQL database, which creates a single point of failure. For greater fault tolerance, the following options are available:
- For non-Geo installations, use one of the fault-tolerant PostgreSQL setups.
- For Geo instances, either:
- Set up a separate PostgreSQL instance.
- Use a cloud-managed PostgreSQL service. AWS Relational Database Service) is recommended.
To complete this section you will need:
- 1 Praefect node
- 1 PostgreSQL server (PostgreSQL 11 or newer)
- An SQL user with permissions to create databases
During this section, we will configure the PostgreSQL server, from the Praefect
node, using psql which is installed by Omnibus GitLab.
-
SSH into the Praefect node and login as root:
sudo -i -
Connect to the PostgreSQL server with administrative access. This is likely the
postgresuser. The databasetemplate1is used because it is created by default on all PostgreSQL servers./opt/gitlab/embedded/bin/psql -U postgres -d template1 -h POSTGRESQL_SERVER_ADDRESSCreate a new user
praefectwhich will be used by Praefect. ReplacePRAEFECT_SQL_PASSWORDwith the strong password you generated in the preparation step.CREATE ROLE praefect WITH LOGIN CREATEDB PASSWORD 'PRAEFECT_SQL_PASSWORD'; -
Reconnect to the PostgreSQL server, this time as the
praefectuser:/opt/gitlab/embedded/bin/psql -U praefect -d template1 -h POSTGRESQL_SERVER_ADDRESSCreate a new database
praefect_production. By creating the database while connected as thepraefectuser, we are confident they have access.CREATE DATABASE praefect_production WITH ENCODING=UTF8;
The database used by Praefect is now configured.
PgBouncer
To reduce PostgreSQL resource consumption, you should set up and configure
PgBouncer in front of the PostgreSQL instance. To do
this, replace value of the POSTGRESQL_SERVER_ADDRESS with corresponding IP or host
address of the PgBouncer instance.
This documentation doesn't provide PgBouncer installation instructions, you can:
- Find instructions on the official website.
- Use a Docker image.
In addition to base PgBouncer configuration options, set the following values:
-
The Praefect PostgreSQL database in the
[databases]section:[databases] * = host=POSTGRESQL_SERVER_ADDRESS port=5432 auth_user=praefect -
pool_modeandignore_startup_parametersin the[pgbouncer]section:[pgbouncer] pool_mode = transaction ignore_startup_parameters = extra_float_digits
The praefect user and its password should be included in the file (default is
userlist.txt) used by PgBouncer if the auth_file
configuration option is set.
NOTE: Note:
By default PgBouncer uses port 6432 to accept incoming
connections. You can change it by setting the listen_port
configuration option. We recommend setting it to the default port value (5432) used by
PostgreSQL instances. Otherwise you should change the configuration parameter
praefect['database_port'] for each Praefect instance to the correct value.
Praefect
To complete this section you will need:
- Configured PostgreSQL server, including:
- IP/host address (
POSTGRESQL_SERVER_ADDRESS) - password (
PRAEFECT_SQL_PASSWORD)
- IP/host address (
Praefect should be run on a dedicated node. Do not run Praefect on the application server, or a Gitaly node.
-
SSH into the Praefect node and login as root:
sudo -i -
Disable all other services by editing
/etc/gitlab/gitlab.rb:# Disable all other services on the Praefect node postgresql['enable'] = false redis['enable'] = false nginx['enable'] = false alertmanager['enable'] = false prometheus['enable'] = false grafana['enable'] = false puma['enable'] = false sidekiq['enable'] = false gitlab_workhorse['enable'] = false gitaly['enable'] = false # Enable only the Praefect service praefect['enable'] = true # Prevent database connections during 'gitlab-ctl reconfigure' gitlab_rails['rake_cache_clear'] = false gitlab_rails['auto_migrate'] = false -
Configure Praefect to listen on network interfaces by editing
/etc/gitlab/gitlab.rb:praefect['listen_addr'] = '0.0.0.0:2305' # Enable Prometheus metrics access to Praefect. You must use firewalls # to restrict access to this address/port. praefect['prometheus_listen_addr'] = '0.0.0.0:9652' -
Configure a strong
auth_tokenfor Praefect by editing/etc/gitlab/gitlab.rb. This will be needed by clients outside the cluster (like GitLab Shell) to communicate with the Praefect cluster :praefect['auth_token'] = 'PRAEFECT_EXTERNAL_TOKEN' -
Configure Praefect to connect to the PostgreSQL database by editing
/etc/gitlab/gitlab.rb.You will need to replace
POSTGRESQL_SERVER_ADDRESSwith the IP/host address of the database, andPRAEFECT_SQL_PASSWORDwith the strong password set above.praefect['database_host'] = 'POSTGRESQL_SERVER_ADDRESS' praefect['database_port'] = 5432 praefect['database_user'] = 'praefect' praefect['database_password'] = 'PRAEFECT_SQL_PASSWORD' praefect['database_dbname'] = 'praefect_production'If you want to use a TLS client certificate, the options below can be used:
# Connect to PostreSQL using a TLS client certificate # praefect['database_sslcert'] = '/path/to/client-cert' # praefect['database_sslkey'] = '/path/to/client-key' # Trust a custom certificate authority # praefect['database_sslrootcert'] = '/path/to/rootcert'By default Praefect will refuse to make an unencrypted connection to PostgreSQL. You can override this by uncommenting the following line:
# praefect['database_sslmode'] = 'disable' -
Configure the Praefect cluster to connect to each Gitaly node in the cluster by editing
/etc/gitlab/gitlab.rb.The virtual storage's name must match the configured storage name in GitLab configuration. In a later step, we configure the storage name as
defaultso we usedefaulthere as well. This cluster has three Gitaly nodesgitaly-1,gitaly-2, andgitaly-3, which will be replicas of each other.CAUTION: Caution: If you have data on an already existing storage called
default, you should configure the virtual storage with another name and migrate the data to the Praefect storage afterwards.Replace
PRAEFECT_INTERNAL_TOKENwith a strong secret, which will be used by Praefect when communicating with Gitaly nodes in the cluster. This token is distinct from thePRAEFECT_EXTERNAL_TOKEN.Replace
GITALY_HOSTwith the IP/host address of the each Gitaly node.More Gitaly nodes can be added to the cluster to increase the number of replicas. More clusters can also be added for very large GitLab instances.
NOTE: Note: The
gitaly-1node is currently denoted the primary. This can be used to manually fail from one node to another. This will be removed in the future.# Name of storage hash must match storage name in git_data_dirs on GitLab # server ('praefect') and in git_data_dirs on Gitaly nodes ('gitaly-1') praefect['virtual_storages'] = { 'default' => { 'gitaly-1' => { 'address' => 'tcp://GITALY_HOST:8075', 'token' => 'PRAEFECT_INTERNAL_TOKEN', 'primary' => true }, 'gitaly-2' => { 'address' => 'tcp://GITALY_HOST:8075', 'token' => 'PRAEFECT_INTERNAL_TOKEN' }, 'gitaly-3' => { 'address' => 'tcp://GITALY_HOST:8075', 'token' => 'PRAEFECT_INTERNAL_TOKEN' } } } -
Introduced in GitLab 13.1 and later, enable distribution of reads.
-
Save the changes to
/etc/gitlab/gitlab.rband reconfigure Praefect:gitlab-ctl reconfigure -
To ensure that Praefect has updated its Prometheus listen address, restart Gitaly:
gitlab-ctl restart praefect -
Verify that Praefect can reach PostgreSQL:
sudo -u git /opt/gitlab/embedded/bin/praefect -config /var/opt/gitlab/praefect/config.toml sql-pingIf the check fails, make sure you have followed the steps correctly. If you edit
/etc/gitlab/gitlab.rb, remember to runsudo gitlab-ctl reconfigureagain before trying thesql-pingcommand.
The steps above must be completed for each Praefect node!
Enabling TLS support
Introduced in GitLab 13.2.
Praefect supports TLS encryption. To communicate with a Praefect instance that listens for secure connections, you must:
- Use a
tls://URL scheme in thegitaly_addressof the corresponding storage entry in the GitLab configuration. - Bring your own certificates because this isn't provided automatically. The certificate corresponding to each Praefect server must be installed on that Praefect server.
Additionally the certificate, or its certificate authority, must be installed on all Gitaly servers and on all Praefect clients that communicate with it following the procedure described in GitLab custom certificate configuration (and repeated below).
Note the following:
-
The certificate must specify the address you use to access the Praefect server. If addressing the Praefect server by:
- Hostname, you can either use the Common Name field for this, or add it as a Subject Alternative Name.
- IP address, you must add it as a Subject Alternative Name to the certificate.
-
You can configure Praefect servers with both an unencrypted listening address
listen_addrand an encrypted listening addresstls_listen_addrat the same time. This allows you to do a gradual transition from unencrypted to encrypted traffic, if necessary.
To configure Praefect with TLS:
For Omnibus GitLab
-
Create certificates for Praefect servers.
-
On the Praefect servers, create the
/etc/gitlab/ssldirectory and copy your key and certificate there:sudo mkdir -p /etc/gitlab/ssl sudo chmod 755 /etc/gitlab/ssl sudo cp key.pem cert.pem /etc/gitlab/ssl/ sudo chmod 644 key.pem cert.pem -
Edit
/etc/gitlab/gitlab.rband add:praefect['tls_listen_addr'] = "0.0.0.0:3305" praefect['certificate_path'] = "/etc/gitlab/ssl/cert.pem" praefect['key_path'] = "/etc/gitlab/ssl/key.pem" -
Save the file and reconfigure GitLab.
-
On the Praefect clients (including each Gitaly server), copy the certificates, or their certificate authority, into
/etc/gitlab/trusted-certs:sudo cp cert.pem /etc/gitlab/trusted-certs/ -
On the Praefect clients (except Gitaly servers), edit
git_data_dirsin/etc/gitlab/gitlab.rbas follows:git_data_dirs({ 'default' => { 'gitaly_address' => 'tls://praefect1.internal:3305' }, 'storage1' => { 'gitaly_address' => 'tls://praefect2.internal:3305' }, }) -
Save the file and reconfigure GitLab.
For installations from source
-
Create certificates for Praefect servers.
-
On the Praefect servers, create the
/etc/gitlab/ssldirectory and copy your key and certificate there:sudo mkdir -p /etc/gitlab/ssl sudo chmod 755 /etc/gitlab/ssl sudo cp key.pem cert.pem /etc/gitlab/ssl/ sudo chmod 644 key.pem cert.pem -
On the Praefect clients (including each Gitaly server), copy the certificates, or their certificate authority, into the system trusted certificates:
sudo cp cert.pem /usr/local/share/ca-certificates/praefect.crt sudo update-ca-certificates -
On the Praefect clients (except Gitaly servers), edit
storagesin/home/git/gitlab/config/gitlab.ymlas follows:gitlab: repositories: storages: default: gitaly_address: tls://praefect1.internal:3305 path: /some/dummy/path storage1: gitaly_address: tls://praefect2.internal:3305 path: /some/dummy/pathNOTE: Note:
/some/dummy/pathshould be set to a local folder that exists, however no data will be stored in this folder. This will no longer be necessary after this issue is resolved. -
Save the file and restart GitLab.
-
Copy all Praefect server certificates, or their certificate authority, to the system trusted certificates on each Gitaly server so the Praefect server will trust the certificate when called by Gitaly servers:
sudo cp cert.pem /usr/local/share/ca-certificates/praefect.crt sudo update-ca-certificates -
Edit
/home/git/praefect/config.tomland add:tls_listen_addr = '0.0.0.0:3305' [tls] certificate_path = '/etc/gitlab/ssl/cert.pem' key_path = '/etc/gitlab/ssl/key.pem' -
Save the file and restart GitLab.
Gitaly
NOTE: Note: Complete these steps for each Gitaly node.
To complete this section you will need:
- Configured Praefect node
- 3 (or more) servers, with GitLab installed, to be configured as Gitaly nodes. These should be dedicated nodes, do not run other services on these nodes.
Every Gitaly server assigned to the Praefect cluster needs to be configured. The configuration is the same as a normal standalone Gitaly server, except:
- the storage names are exposed to Praefect, not GitLab
- the secret token is shared with Praefect, not GitLab
The configuration of all Gitaly nodes in the Praefect cluster can be identical, because we rely on Praefect to route operations correctly.
Particular attention should be shown to:
- the
gitaly['auth_token']configured in this section must match thetokenvalue underpraefect['virtual_storages']on the Praefect node. This was set in the previous section. This document uses the placeholderPRAEFECT_INTERNAL_TOKENthroughout. - the storage names in
git_data_dirsconfigured in this section must match the storage names underpraefect['virtual_storages']on the Praefect node. This was set in the previous section. This document usesgitaly-1,gitaly-2, andgitaly-3as Gitaly storage names.
For more information on Gitaly server configuration, see our Gitaly documentation.
-
SSH into the Gitaly node and login as root:
sudo -i -
Disable all other services by editing
/etc/gitlab/gitlab.rb:# Disable all other services on the Praefect node postgresql['enable'] = false redis['enable'] = false nginx['enable'] = false grafana['enable'] = false puma['enable'] = false sidekiq['enable'] = false gitlab_workhorse['enable'] = false prometheus_monitoring['enable'] = false # Enable only the Gitaly service gitaly['enable'] = true # Enable Prometheus if needed prometheus['enable'] = true # Prevent database connections during 'gitlab-ctl reconfigure' gitlab_rails['rake_cache_clear'] = false gitlab_rails['auto_migrate'] = false -
Configure Gitaly to listen on network interfaces by editing
/etc/gitlab/gitlab.rb:# Make Gitaly accept connections on all network interfaces. # Use firewalls to restrict access to this address/port. gitaly['listen_addr'] = '0.0.0.0:8075' # Enable Prometheus metrics access to Gitaly. You must use firewalls # to restrict access to this address/port. gitaly['prometheus_listen_addr'] = '0.0.0.0:9236' -
Configure a strong
auth_tokenfor Gitaly by editing/etc/gitlab/gitlab.rb. This will be needed by clients to communicate with this Gitaly nodes. Typically, this token will be the same for all Gitaly nodes.gitaly['auth_token'] = 'PRAEFECT_INTERNAL_TOKEN' -
Configure the GitLab Shell
secret_token, andinternal_api_urlwhich are needed forgit pushoperations.If you have already configured Gitaly on its own server
gitlab_shell['secret_token'] = 'GITLAB_SHELL_SECRET_TOKEN' # Configure the gitlab-shell API callback URL. Without this, `git push` will # fail. This can be your front door GitLab URL or an internal load balancer. # Examples: 'https://gitlab.example.com', 'http://1.2.3.4' gitlab_rails['internal_api_url'] = 'http://GITLAB_HOST' -
Configure the storage location for Git data by setting
git_data_dirsin/etc/gitlab/gitlab.rb. Each Gitaly node should have a unique storage name (such asgitaly-1).Instead of configuring
git_data_dirsuniquely for each Gitaly node, it is often easier to have include the configuration for all Gitaly nodes on every Gitaly node. This is supported because the Praefectvirtual_storagesconfiguration maps each storage name (such asgitaly-1) to a specific node, and requests are routed accordingly. This means every Gitaly node in your fleet can share the same configuration.# You can include the data dirs for all nodes in the same config, because # Praefect will only route requests according to the addresses provided in the # prior step. git_data_dirs({ "gitaly-1" => { "path" => "/var/opt/gitlab/git-data" }, "gitaly-2" => { "path" => "/var/opt/gitlab/git-data" }, "gitaly-3" => { "path" => "/var/opt/gitlab/git-data" } }) -
Save the changes to
/etc/gitlab/gitlab.rband reconfigure Gitaly:gitlab-ctl reconfigure -
To ensure that Gitaly has updated its Prometheus listen address, restart Gitaly:
gitlab-ctl restart gitaly
The steps above must be completed for each Gitaly node!
After all Gitaly nodes are configured, you can run the Praefect connection checker to verify Praefect can connect to all Gitaly servers in the Praefect config.
-
SSH into the Praefect node and run the Praefect connection checker:
sudo /opt/gitlab/embedded/bin/praefect -config /var/opt/gitlab/praefect/config.toml dial-nodes
Load Balancer
In a highly available Gitaly configuration, a load balancer is needed to route internal traffic from the GitLab application to the Praefect nodes. The specifics on which load balancer to use or the exact configuration is beyond the scope of the GitLab documentation.
NOTE: Note:
The load balancer must be configured to accept traffic from the Gitaly nodes in
addition to the GitLab nodes. Some requests handled by
gitaly-ruby sidecar processes call into the main Gitaly
process. gitaly-ruby uses the Gitaly address set in the GitLab server's
git_data_dirs setting to make this connection.
We hope that if you’re managing HA systems like GitLab, you have a load balancer of choice already. Some examples include HAProxy (open-source), Google Internal Load Balancer, AWS Elastic Load Balancer, F5 Big-IP LTM, and Citrix Net Scaler. This documentation will outline what ports and protocols you need configure.
| LB Port | Backend Port | Protocol |
|---|---|---|
| 2305 | 2305 | TCP |
GitLab
To complete this section you will need:
The Praefect cluster needs to be exposed as a storage location to the GitLab
application. This is done by updating the git_data_dirs.
Particular attention should be shown to:
- the storage name added to
git_data_dirsin this section must match the storage name underpraefect['virtual_storages']on the Praefect node. This was set in the Praefect section of this guide. This document usesstorage-1as the Praefect storage name.
-
SSH into the GitLab node and login as root:
sudo -i -
Configure the
external_urlso that files could be served by GitLab by proper endpoint access by editing/etc/gitlab/gitlab.rb:You will need to replace
GITLAB_SERVER_URLwith the real external facing URL on which current GitLab instance is serving:external_url 'GITLAB_SERVER_URL' -
Disable the default Gitaly service running on the GitLab host. It won't be needed as GitLab will connect to the configured cluster.
CAUTION: Caution: If you have existing data stored on the default Gitaly storage, you should migrate the data your Praefect storage first.
gitaly['enable'] = false -
Add the Praefect cluster as a storage location by editing
/etc/gitlab/gitlab.rb.You will need to replace:
LOAD_BALANCER_SERVER_ADDRESSwith the IP address or hostname of the load balancer.PRAEFECT_EXTERNAL_TOKENwith the real secret
git_data_dirs({ "default" => { "gitaly_address" => "tcp://LOAD_BALANCER_SERVER_ADDRESS:2305", "gitaly_token" => 'PRAEFECT_EXTERNAL_TOKEN' } }) -
Configure the
gitlab_shell['secret_token']so that callbacks from Gitaly nodes during agit pushare properly authenticated by editing/etc/gitlab/gitlab.rb:You will need to replace
GITLAB_SHELL_SECRET_TOKENwith the real secret.gitlab_shell['secret_token'] = 'GITLAB_SHELL_SECRET_TOKEN' -
Add Prometheus monitoring settings by editing
/etc/gitlab/gitlab.rb.You will need to replace:
PRAEFECT_HOSTwith the IP address or hostname of the Praefect nodeGITALY_HOSTwith the IP address or hostname of each Gitaly node
prometheus['scrape_configs'] = [ { 'job_name' => 'praefect', 'static_configs' => [ 'targets' => [ 'PRAEFECT_HOST:9652', # praefect-1 'PRAEFECT_HOST:9652', # praefect-2 'PRAEFECT_HOST:9652', # praefect-3 ] ] }, { 'job_name' => 'praefect-gitaly', 'static_configs' => [ 'targets' => [ 'GITALY_HOST:9236', # gitaly-1 'GITALY_HOST:9236', # gitaly-2 'GITALY_HOST:9236', # gitaly-3 ] ] } ] -
Save the changes to
/etc/gitlab/gitlab.rband reconfigure GitLab:gitlab-ctl reconfigure -
Verify each
gitlab-shellon each Gitaly instance can reach GitLab. On each Gitaly instance run:/opt/gitlab/embedded/service/gitlab-shell/bin/check -config /opt/gitlab/embedded/service/gitlab-shell/config.yml -
Verify that GitLab can reach Praefect:
gitlab-rake gitlab:gitaly:check -
Check in Admin Area > Settings > Repository > Repository storage that the Praefect storage is configured to store new repositories. Following this guide, the
defaultstorage should have weight 100 to store all new repositories. -
Verify everything is working by creating a new project. Check the "Initialize repository with a README" box so that there is content in the repository that viewed. If the project is created, and you can see the README file, it works!
Grafana
Grafana is included with GitLab, and can be used to monitor your Praefect cluster. See Grafana Dashboard Service for detailed documentation.
To get started quickly:
-
SSH into the GitLab node and login as root:
sudo -i -
Enable the Grafana login form by editing
/etc/gitlab/gitlab.rb.grafana['disable_login_form'] = false -
Save the changes to
/etc/gitlab/gitlab.rband reconfigure GitLab:gitlab-ctl reconfigure -
Set the Grafana admin password. This command will prompt you to enter a new password:
gitlab-ctl set-grafana-password -
In your web browser, open
/-/grafana(e.g.https://gitlab.example.com/-/grafana) on your GitLab server.Login using the password you set, and the username
admin. -
Go to Explore and query
gitlab_build_infoto verify that you are getting metrics from all your machines.
Congratulations! You've configured an observable highly available Praefect cluster.
Distributed reads
Praefect supports distribution of read operations across Gitaly nodes that are configured for the virtual node.
The feature is enabled by default. To disable distributed reads, the gitaly_distributed_reads
feature flag must be disabled in a Ruby console:
Feature.disable(:gitaly_distributed_reads)
If enabled, all RPCs marked with ACCESSOR option like
GetBlob
are redirected to an up to date and healthy Gitaly node.
Up to date in this context means that:
- There is no replication operations scheduled for this node.
- The last replication operation is in completed state.
If there is no such nodes, or any other error occurs during node selection, the primary node will be chosen to serve the request.
To track distribution of read operations, you can use the gitaly_praefect_read_distribution
Prometheus counter metric. It has two labels:
virtual_storage.storage.
They reflect configuration defined for this instance of Praefect.
Strong consistency
Praefect guarantees eventual consistency by replicating all writes to secondary nodes after the write to the primary Gitaly node has happened.
Praefect can instead provide strong consistency by creating a transaction and writing changes to all Gitaly nodes at once. Strong consistency is currently in alpha and not enabled by default. If enabled, transactions are only available for a subset of RPCs. For more information, see the strong consistency epic.
To enable strong consistency:
- In GitLab 13.3 and later, reference transactions are enabled by default with
a primary-wins strategy. This strategy causes all transactions to succeed for
the primary and thus does not ensure strong consistency. To enable strong
consistency, disable the
:gitaly_reference_transactions_primary_winsfeature flag. - In GitLab 13.2, enable the
:gitaly_reference_transactionsfeature flag. - In GitLab 13.1, enable the
:gitaly_reference_transactionsand:gitaly_hooks_rpcfeature flags.
Changing feature flags requires access to the Rails console. In the Rails console, enable or disable the flags as required. For example:
Feature.enable(:gitaly_reference_transactions)
Feature.disable(:gitaly_reference_transactions_primary_wins)
To monitor strong consistency, you can use the following Prometheus metrics:
gitaly_praefect_transactions_total: Number of transactions created and voted on.gitaly_praefect_subtransactions_per_transaction_total: Number of times nodes cast a vote for a single transaction. This can happen multiple times if multiple references are getting updated in a single transaction.gitaly_praefect_voters_per_transaction_total: Number of Gitaly nodes taking part in a transaction.gitaly_praefect_transactions_delay_seconds: Server-side delay introduced by waiting for the transaction to be committed.gitaly_hook_transaction_voting_delay_seconds: Client-side delay introduced by waiting for the transaction to be committed.
Automatic failover and leader election
Praefect regularly checks the health of each backend Gitaly node. This information can be used to automatically failover to a new primary node if the current primary node is found to be unhealthy.
- PostgreSQL (recommended): Enabled by default, and equivalent to:
praefect['failover_election_strategy'] = sql. This configuration option will allow multiple Praefect nodes to coordinate via the PostgreSQL database to elect a primary Gitaly node. This configuration will cause Praefect nodes to elect a new primary, monitor its health, and elect a new primary if the current one has not been reachable in 10 seconds by a majority of the Praefect nodes. - Manual: Automatic failover is disabled. The primary node can be
reconfigured in
/etc/gitlab/gitlab.rbon the Praefect node. Modify thepraefect['virtual_storages']field by moving theprimary = trueto promote a different Gitaly node to primary. In the steps above,gitaly-1was set to the primary. Requirespraefect['failover_enabled'] = falsein the configuration. - Memory: Enabled by setting
praefect['failover_election_strategy'] = 'local'in/etc/gitlab/gitlab.rbon the Praefect node. If a sufficient number of health checks fail for the current primary backend Gitaly node, and new primary will be elected. Do not use with multiple Praefect nodes! Using with multiple Praefect nodes is likely to result in a split brain.
It is likely that we will implement support for Consul, and a cloud native strategy in the future.
Primary Node Failure
Gitaly Cluster recovers from a failing primary Gitaly node by promoting a healthy secondary as the new primary.
To minimize data loss, Gitaly Cluster:
- Switches repositories that are outdated on the new primary to read-only mode.
- Elects the secondary with the least unreplicated writes from the primary to be the new primary. Because there can still be some unreplicated writes, data loss can occur.
Read-only mode
- Introduced in GitLab 13.0 as generally available.
- Between GitLab 13.0 and GitLab 13.2, read-only mode applied to the whole virtual storage and occurred whenever failover occurred.
- In GitLab 13.3 and later, read-only mode applies on a per-repository basis and only occurs if a new primary is out of date.
When Gitaly Cluster switches to a new primary, repositories enter read-only mode if they are out of date. This can happen after failing over to an outdated secondary. Read-only mode eases data recovery efforts by preventing writes that may conflict with the unreplicated writes on other nodes.
To enable writes again, an administrator can:
- Check for data loss.
- Attempt to recover missing data.
- Either enable writes in the virtual storage or accept data loss if necessary, depending on the version of GitLab.
Check for data loss
The Praefect dataloss sub-command identifies replicas that are likely to be outdated. This is
useful for identifying potential data loss after a failover. The following parameters are
available:
-virtual-storagethat specifies which virtual storage to check. The default behavior is to display outdated replicas of read-only repositories as they generally require administrator action.- In GitLab 13.3 and later,
-partially-replicatedthat specifies whether to display a list of outdated replicas of writable repositories.
NOTE: Note:
dataloss is still in beta and the output format is subject to change.
To check for outdated replicas of read-only repositories, run:
sudo /opt/gitlab/embedded/bin/praefect -config /var/opt/gitlab/praefect/config.toml dataloss [-virtual-storage <virtual-storage>]
Every configured virtual storage is checked if none is specified:
sudo /opt/gitlab/embedded/bin/praefect -config /var/opt/gitlab/praefect/config.toml dataloss
The number of potentially unapplied changes to repositories is listed for each replica. Listed repositories might have the latest changes but it is not guaranteed. Only outdated replicas of read-only repositories are listed by default. For example:
Virtual storage: default
Primary: gitaly-3
Outdated repositories:
@hashed/2c/62/2c624232cdd221771294dfbb310aca000a0df6ac8b66b696d90ef06fdefb64a3.git (read-only):
gitaly-2 is behind by 1 change or less
gitaly-3 is behind by 2 changes or less
A confirmation is printed out when every repository is writable. For example:
Virtual storage: default
Primary: gitaly-1
All repositories are writable!
Outdated replicas of writable repositories
Introduced in GitLab 13.3.
To also list information for outdated replicas of writable repositories, use the
-partially-replicated parameter.
A repository is writable if the primary has the latest changes. Secondaries might be temporarily outdated while they are waiting to replicate the latest changes.
sudo /opt/gitlab/embedded/bin/praefect -config /var/opt/gitlab/praefect/config.toml dataloss [-virtual-storage <virtual-storage>] [-partially-replicated]
Example output:
Virtual storage: default
Primary: gitaly-3
Outdated repositories:
@hashed/2c/62/2c624232cdd221771294dfbb310aca000a0df6ac8b66b696d90ef06fdefb64a3.git (read-only):
gitaly-2 is behind by 1 change or less
gitaly-3 is behind by 2 changes or less
@hashed/4b/22/4b227777d4dd1fc61c6f884f48641d02b4d121d3fd328cb08b5531fcacdabf8a.git (writable):
gitaly-2 is behind by 1 change or less
With the -partially-replicated flag set, a confirmation is printed out if every replica is fully up to date.
For example:
Virtual storage: default
Primary: gitaly-1
All repositories are up to date!
Check repository checksums
To check a project's repository checksums across on all Gitaly nodes, run the replicas Rake task on the main GitLab node.
Recover missing data
The Praefect reconcile sub-command can be used to recover unreplicated changes from another replica.
The source must be on a later version than the target storage.
sudo /opt/gitlab/embedded/bin/praefect -config /var/opt/gitlab/praefect/config.toml reconcile -virtual <virtual-storage> -reference <up-to-date-storage> -target <outdated-storage> -f
Refer to Gitaly node recovery section for more details on the reconcile sub-command.
Enable writes or accept data loss
Praefect provides the following subcommands to re-enable writes:
-
In GitLab 13.2 and earlier,
enable-writesto re-enable virtual storage for writes after data recovery attempts.sudo /opt/gitlab/embedded/bin/praefect -config /var/opt/gitlab/praefect/config.toml enable-writes -virtual-storage <virtual-storage> -
In GitLab 13.3 and later,
accept-datalossto accept data loss and re-enable writes for repositories after data recovery attempts have failed. Accepting data loss causes current version of the repository on the authoritative storage to be considered latest. Other storages are brought up to date with the authoritative storage by scheduling replication jobs.sudo /opt/gitlab/embedded/bin/praefect -config /var/opt/gitlab/praefect/config.toml accept-dataloss -virtual-storage <virtual-storage> -repository <relative-path> -authoritative-storage <storage-name>
CAUTION: Caution:
accept-dataloss causes permanent data loss by overwriting other versions of the repository. Data
recovery efforts must be performed before using it.
Gitaly node recovery
When a secondary Gitaly node fails and is no longer able to replicate changes, it starts to drift from the primary Gitaly node. If the failed Gitaly node eventually recovers, it needs to be reconciled with the primary Gitaly node. The primary Gitaly node is considered the single source of truth for the state of a shard.
The Praefect reconcile sub-command allows for the manual reconciliation between a secondary
Gitaly node and the current primary Gitaly node.
Run the following command on the Praefect server after all placeholders
(<virtual-storage> and <target-storage>) have been replaced:
sudo /opt/gitlab/embedded/bin/praefect -config /var/opt/gitlab/praefect/config.toml reconcile -virtual <virtual-storage> -target <target-storage>
- Replace the placeholder
<virtual-storage>with the virtual storage containing the Gitaly node storage to be checked. - Replace the placeholder
<target-storage>with the Gitaly storage name.
The command will return a list of repositories that were found to be inconsistent against the current primary. Each of these inconsistencies will also be logged with an accompanying replication job ID.
Migrating existing repositories to Praefect
If your GitLab instance already has repositories, these won't be migrated automatically.
Repositories may be moved from one storage location using the Project repository storage moves API:
curl --request POST --header "Private-Token: <your_access_token>" --header "Content-Type: application/json" \
--data '{"destination_storage_name":"praefect"}' "https://gitlab.example.com/api/v4/projects/123/repository_storage_moves"
Debugging Praefect
If you receive an error, check /var/log/gitlab/gitlab-rails/production.log.
Here are common errors and potential causes:
- 500 response code
- ActionView::Template::Error (7:permission denied)
praefect['auth_token']andgitlab_rails['gitaly_token']do not match on the GitLab server.
- Unable to save project. Error: 7:permission denied
- Secret token in
praefect['storage_nodes']on GitLab server does not match the value ingitaly['auth_token']on one or more Gitaly servers.
- Secret token in
- ActionView::Template::Error (7:permission denied)
- 503 response code
- GRPC::Unavailable (14:failed to connect to all addresses)
- GitLab was unable to reach Praefect.
- GRPC::Unavailable (14:all SubCons are in TransientFailure...)
- Praefect cannot reach one or more of its child Gitaly nodes. Try running the Praefect connection checker to diagnose.
- GRPC::Unavailable (14:failed to connect to all addresses)